Ransomware Hits You Where It Hurts
8th June 2016
Ransomware is the current hot potato when it comes to viruses and malware. Like other forms of malware, things tend to start with dodgy downloads or e-mail attachments that are opened by users that are either tricked into believing something is from a legitimate source, or isn't "aware" enough of the risks to think there is any harm in opening or clicking on something. Where Ransomware varies from other forms, but cruelly so is the rapidly destructive & financially demanding nature of the malware.
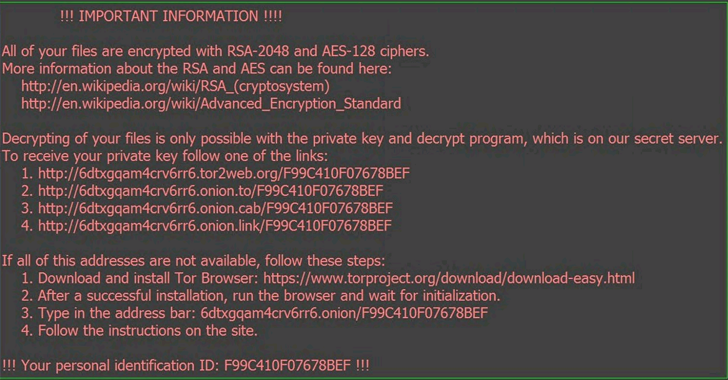 (Example of a typical Ransomware Screen)
(Example of a typical Ransomware Screen)
Typically Ransomware encrypts your data and files using a unique encryption key - or in other words, it scrambles the data (your files, documents etc) using a method that means only the person who did it (in this case, the authors of the malware) can decrypt the data. The money part is then quite simple yet costly - if you don't have a good and safe backup (and frankly, most people regrettably don't), the net result will be either losing data or paying someone to effectively get the knowledge of that method.
It has become such an issue that it now ranks as the most common issue for malware, and we see more and more evidence of people bringing in infected computers that have been hit by some form of ransomware, as well as pretty frequent press coverage.
The BBC has reported an issue just today where a univesity in Canada ended up paying around £10,800 to the authors of some ransomware so thery could decrypt some data and restore access to files that had been encrypted. The university had even spent some time trying to decrypt the data themselves before giving up and paying up.
The BBC report also suggests that over 100 computers had been compromised in this latest batch, and that even once they have the decryption keys, decrypting and getting things back to normal isn't by any means a fast job, so in addition to the existing disruption, the financial cost and of course the rather poor PR, they've got even more time to spend getting things resolved - and no doubt need to have a serious review of the IT systems and security in place.
So how can you minimse your risk?
Essentially by following the usual advice...
PLEASE get a proper backup - that doesn't mean a USB Flash Key or Drive you connect (and leave connected) to the computer. Get proper remote backup servics (our sister company and many others offer this type of service).
Make sure you NEVER open an attachment in an e-mail that you're not expecting. Be really cautious.
Absolutely make sure you have a paid for, up to date anti-virus product - the free products aren't bad in many cases, but often come with slow updates (the compromise for them being free). However, don't assume that anti-malware/anti-virus software will catch issues and save you - ultimately malware is fast moving and thus often a probelm exists for a while before detection systems are updated to spot them.
What to do if you think it's too late?
Stop using your computer.Immediately. Shut it down. Although the temptation exists to "just finish things off" or "get along for the weekend" the reality is that these programmes sit in the background, and are rarely noticable - they normally only pop up and declare themselves to exist after encryption is completed, so turning off the computer can help minimise your exposure.
Get your computer checked out by a competent IT Support company - they should be able to identify if you have any malware and what has happened - and should also be able to recover data if you're not yet fully encrypted. If you are, they may not be able to completely resolve this unless you have good backups etc. However we do strongly advise you get professional help because new malware is clever and very destructive.